Inheriti Deep-Dive Series // 004 : Everything You Didn’t Realize You Needed from a Digital Inheritance Platform

Welcome to the fourth article in our Inheriti Deep-Dive Series.
What do you need from a Digital Inheritance platform you can trust?
So, what requirements would a really world-class digital inheritance platform need to be able to satisfy?
After all, if you had a clear idea of the gold standard features and benefits you were looking for, you’d be more likely to recognize an outstanding platform when you see one, right?
In this article, we’ll outline all the characteristics that a digital inheritance platform truly deserving of your trust and attention would need to have …
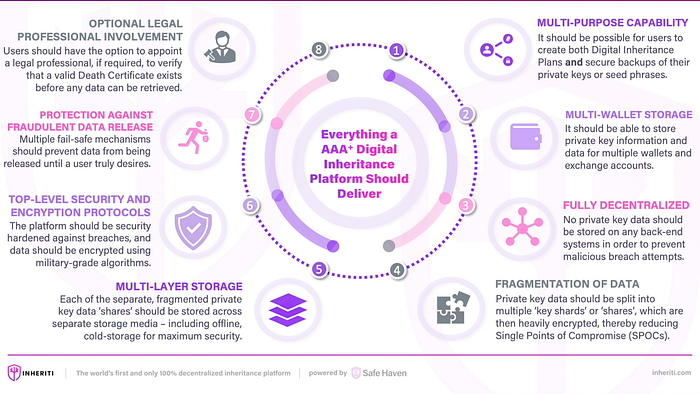
- Multi-Purpose Capability (Digital Inheritance and Personal Backup) — It should be possible for users to utilize many of the same security and produce features inherent in the platform in order to create both digital inheritance plans and secure backups of their private keys or seed phrases.
- Multi-Wallet Storage — The solution should allow you to store private key information and data for multiple wallets (catering for both cryptocurrency and NFTs) and exchange accounts as well as any other kind of secret data (e.g. secret family recipes, industrial formulas, GPS coordinates of buried treasure etc.).
- Fully Decentralized — No private key data should be stored on any supplier back-end systems or repositories in order to prevent the retrieval of any secret data arising from human error or malicious breach attempts by third-parties.
- Fragmentation of Data — Private key data should be split into multiple key ‘shards’ or ‘shares’, which are then heavily encrypted, thereby reducing Single Points of Compromise (SPOCs). This means that the required number of secret data ‘shares’ would all need to be both identified and combined — even before any attempt at decryption could be made.
- Multi-Storage Layers — Each of the separate, fragmented private key data ‘shares’ should be stored across separate storage media — including offline, cold-storage for maximum security.
- Top-Level Security Protocols and Encryption — The platform should be security hardened against breaches, and data (in-motion or at-rest) should be heavily encrypted using military-grade algorithms.
- Protection against Premature Data Release– Multiple fail-safe mechanisms should prevent anyone gaining access to any secret data until a user truly desires (and for inheritance plans, until a user has definitely passed).
- Separation of Roles — The platform should be able to distinguish between those trusted individuals who may be tasked with initiating the secret data recovery process from those who you want to retrieve the secret data (i.e. your beneficiaries).
- Optional Legal Professional Involvement —Users should have the option to appoint a suitably qualified legal professional, if required, to act as the formal authority who can verify that a valid Death Certificate exists before the secret data retrieval process can be initiated.
Surely there can’t be a Digital Inheritance solution available that meets ALL of these requirements? …
Can there?
Well, we’re happy to tell you there is.
Introducing Inheriti — The World’s Only Truly Decentralized Digital Inheritance Platform
Inheriti is Safe Haven’s flagship product and is the only truly decentralized (and totally secure) digital inheritance and private key backup solution available in the world.

Our Inheriti Community Edition (CE) version is immediately available with full capability for creating digital inheritance plans and also making secure backups of your private keys / seed phrases.
Those requirements that a really world-class digital inheritance platform would need to meet?
Inheriti meets every single one of them.
Yep.
Every. Single. One.
Find out how in our next article in this series — ‘Inheriti Deep-Dive Series // 005 : Introducing Inheriti — An Overview of Key Features and Benefits … coming very soon!
As always, all of us at Safe Haven want to thank our community for your continued support. Be sure to keep up with our official channels!
Join our Official Telegram Channel: https://t.me/safehavenio
Join our Official Announcements Telegram Channel: https://t.me/safehavenio_announcements
Follow us on Twitter: https://twitter.com/safehavenio and https://twitter.com/inheriti_com
